Malware Exploits Undocumented Google OAuth Endpoint to Hijack Accounts via “Revived” Cookies
In a chilling revelation, security researchers have discovered that several malware families are using an undocumented Google OAuth endpoint called “MultiLogin” to restore expired authentication cookies, allowing cybercriminals to hijack accounts even after action has been taken. such as changing passwords or logging out. This exploit, which was disclosed by a threat actor called PRISMA, has revealed the vulnerability in Google’s authentication system.
In late November 2023, two malwares, Lumma and Rhadamanthys, were reported that claimed to have the ability to restore expired Google authentication cookies, triggering concerns about the security of Google accounts.
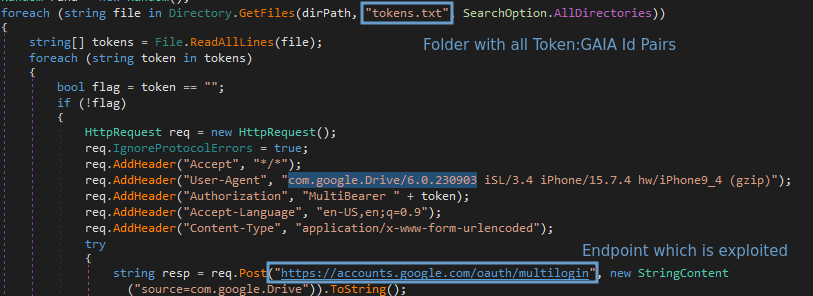
CloudSEK researchers have unraveled the details of the exploit, which uses the undocumented “MultiLogin” Google OAuth endpoint. This endpoint is designed to sync accounts across different Google services by accepting a vector of account IDs and authentication login tokens. The malware extracts tokens and account IDs from Chrome profiles connected to a Google account and uses the stolen information to regenerate expired authentication cookies.
The malware, once installed, extracts crucial information from Chrome profiles, including GAIA ID and encrypted_token. Encrypted tokens are decrypted using a key stored in Chrome’s “Local State” file, which is also used to decrypt passwords saved in the browser. With this information, cybercriminals can regenerate expired cookies, thus maintaining persistent access to compromised accounts.
This exploit allows attackers to bypass common security measures, such as password resets, as cookies can be regenerated even after this process. Persistent access compromises the integrity of Google accounts and raises serious online security concerns.
Given the severity of this threat, it is essential that users be alert and take additional steps to protect their accounts. Additionally, Google is expected to respond with mitigation measures to address this critical vulnerability and protect the security of its users.