Casbaneiro, from the banking malware family, has been observed using user account control (UAC) evasion techniques to gain full administrative privileges on a given machine.
The malicious actors behind Casbaneiro, also known as Metamorfo and Ponteiro, are known for conducting attacks against financial organizations, with a particular focus on organizations in the Latin American region, using the malware, the subject of this article, “Casbaneiro”.
This malware is a banking Trojan, first seen in 2018, through an email spam campaign targeting the Latin American financial sector. According to Sygnia, while the targets of the attacks continue to be the Latin American financial sector, the change in the techniques implemented in current campaigns represent a significant problem for the financial sector.
In more recent attacks, it has been observed that the infection chain starts with spear-phishing emails containing malicious HTML attachments, which redirect the victim to a malicious domain where a RAR file is downloaded with scripts in CMD which executes a PowerShell dropper.
![]()
Among the updates to the tactics, techniques and procedures (TTPS) of the malicious actor group is the evasion technique using user account control (UAC) to execute code without a UAC prompt using “fodhelper.exe”. The above is an executable used by Windows to manage capabilities in its configurations and is commonly used by attackers to achieve UAC evasion.
Typically, the attack is initiated by creating the following registry keys:
- HKCU:Software: Classes-settingsshellopencommand
- HKCU:Software: Classesms-settingsshellopencommandDelegateExecute
- HKCU:Software: Classes-settingsshellopencommand(default)
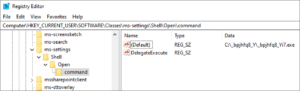
Next, the attacker fills a default subkey with the command line. Once “fodhelper.exe” is executed, either manually or by navigating through “Manage optional features” in Windows, it executes the command line with high-integrity execution, thus bypassing the UAC prompt.
According to Sygnia’s observations, the malicious actors also created a dummy folder in C:Windows[space]system32, and then copied the “fodhelper.exe” into this folder, however, the use of this script was not detected at the time of the investigation. It is very likely that the malicious actor releases the dummy folder to evade antivirus detection or exploit the folder to sideload DLLs with signed Microsoft binaries, to evade UAC.

C2 communication
The HTML at the beginning of the infection chain resolves to an IP of Choopa ASN (45.32.90[.]70) which links to hundreds of additional domains, of these, several were created and resolved to the same IP. In addition, about 40 files with the same HTML file name (attachments_0102.html) were discovered, all of these files were embedded with one of 4 related domains.
It is important to highlight that, according to observations, this would be the third time that the spoofed trusted folder approach has been detected, in recent months, used in campaigns for the delivery of a malware loader called “DBatLoader” as well as the remote access Trojan (RAT) “Warzone RAT” also known as “Ave Maria”.
IOCs
| Type | Indicator |
| Domain | contactofiscal[.]cfd |
| Domain | tributaria[.]website |
| IP | 185.183.98[.]135 |
| IP | 216.238.82[.]27 |
| IP | 45.32.90.70 |
| IP | 139.177.193[.]74 |
| Domain | factudigital[.]cfd |
| Domain | factdigital[.]shop |
| Domain | cgdf[.]shop |
| Domain | serviciofac[.]shop |
| Domain | fiscalcgdf[.]shop |
| Domain | wiqp[.]xyz |
| Domain | live.xtream-ui[.]info |