CISA Adds Ten Known Exploited Vulnerabilities to Catalog
CISA has added ten new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation.
CVE-2013-3163 Microsoft Internet Explorer Memory Corruption Vulnerability
CVE-2014-1776 Microsoft Internet Explorer Memory Corruption Vulnerability
CVE-2017-7494 Samba Remote Code Execution Vulnerability
CVE-2022-42948 Fortra Cobalt Strike User Interface Remote Code Execution Vulnerability
CVE-2022-39197 Fortra Cobalt Strike Teamserver Cross-Site Scripting (XSS) Vulnerability
CVE-2021-30900 Apple iOS, iPadOS, and macOS Out-of-Bounds Write Vulnerability
CVE-2022-38181 Arm Mali GPU Kernel Driver Use-After-Free Vulnerability
CVE-2023-0266 Linux Kernel Use-After-Free Vulnerability
CVE-2022-3038 Google Chrome Use-After-Free Vulnerability
CVE-2022-22706 Arm Mali GPU Kernel Driver Unspecified Vulnerability
These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Note: To view other newly added vulnerabilities in the catalog, click on the arrow in the “Date Added to Catalog” column—which will sort by descending dates.
Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the Known Exploited Vulnerabilities Catalog as a living list of known Common Vulnerabilities and Exposures (CVEs) that carry significant risk to the federal enterprise. BOD 22-01 requires Federal Civilian Executive Branch (FCEB) agencies to remediate identified vulnerabilities by the due date to protect FCEB networks against active threats. See the BOD 22-01 Fact Sheet for more information.
Although BOD 22-01 only applies to FCEB agencies, CISA strongly urges all organizations to reduce their exposure to cyberattacks by prioritizing timely remediation of Catalog vulnerabilities as part of their vulnerability management practice. CISA will continue to add vulnerabilities to the catalog that meet the specified criteria.
Dark Power, nuevo ransomware activo.
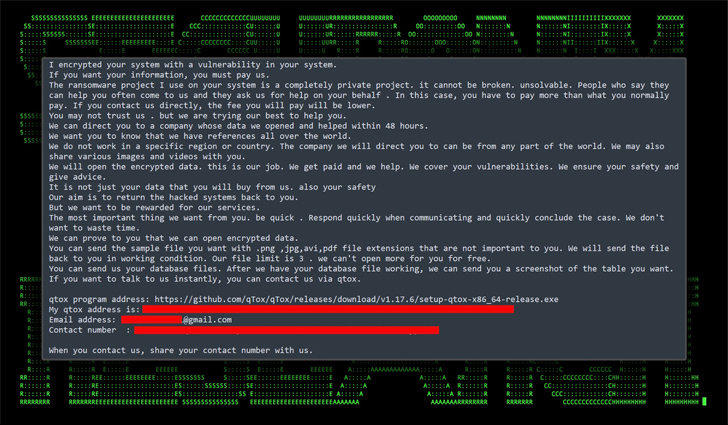
Ha aparecido una nueva operación de ransomware llamado “Dark Power”, y ya ha enumerado a sus primeras víctimas en un sitio de fuga de datos de la dark web, amenazando con publicar los datos si no se paga un rescate. El cifrador de la banda de ransomware tiene una fecha de compilación del 29 de […]
Supply Chain Attack Against 3CXDesktopApp
CISA is aware of open-source reports describing a supply chain attack against 3CX software and their customers. According to the reports, 3CXDesktopApp — a voice and video conferencing app — was trojanized, potentially leading to multi-staged attacks against users employing the vulnerable app.
CISA urges users and organizations to review the following reports for more information, and hunt for the listed indicators of compromise (IOCs) for potential malicious activity:
CrowdStrike: Falcon Platform Detects and Prevents Active Intrusion Campaign Targeting 3CXDesktopApp Customers
SentinelOne: SmoothOperator | Ongoing Campaign Trojanizes 3CXDesktopApp in Supply Chain Attack
Dark Power Nuevo Ransomware Activo

Ha aparecido una nueva operación de ransomware llamada “Dark Power”, y ya ha enumerado a sus primeras víctimas en un sitio de fuga de datos de la dark web, amenazando con publicar los datos si no se paga un rescate. El cifrador de la banda de ransomware tiene una fecha de compilación del 29 de […]
