Solutions
Our Solutions Portfolio combines leading security technologies with disciplined architecture, implementation, and operational support. We focus on outcomes—not
product resale.
Manufacturers
From design to long-term support, we ensure platforms are integrated, optimized, and operationally stable.


Our Technology Partners & Solutions
Strategic alliances with leading cybersecurity providers.
Our Proven Methodology
We follow a step-by-step approach that ensures clarity and measurable results.
Advisory Meeting
Assess architecture and business requirements.
Proposal presentation
Define solution scope and delivery roadmap.
Service Kickoff
Align governance and technical integration plan.
Delivery
Implement, integrate, and validate platforms.
Results Presentation
Review outcomes, performance, and optimization plan.

Service Kickof
Project initiation meeting where expectations are aligned, roles and responsibilities are assigned, and the first operational steps for service execution are established.

Service Delivery
Execution of the services agreed upon in the proposal, which may include consulting, solution implementation, training, or other specific tasks.

Results Presentation
The findings, conclusions, and results obtained during the service execution are presented. In this phase, the benefits achieved are analyzed, and future recommendations may be proposed.
A formal proposal is presented to the client, which includes the recommended solution, the work plan, deliverables, costs, and the execution timeline. The objective is to obtain approval to proceed with the service.
Web Application Firewall (WAF)
A WAF protects your applications by filtering and monitoring HTTP traffic between your apps and the internet.
Monthly health checks.
Third-party integrations.
Custom dashboards.
Task automation.
AI-driven behavioral analysis.
Config optimization.
24/7/365 support.

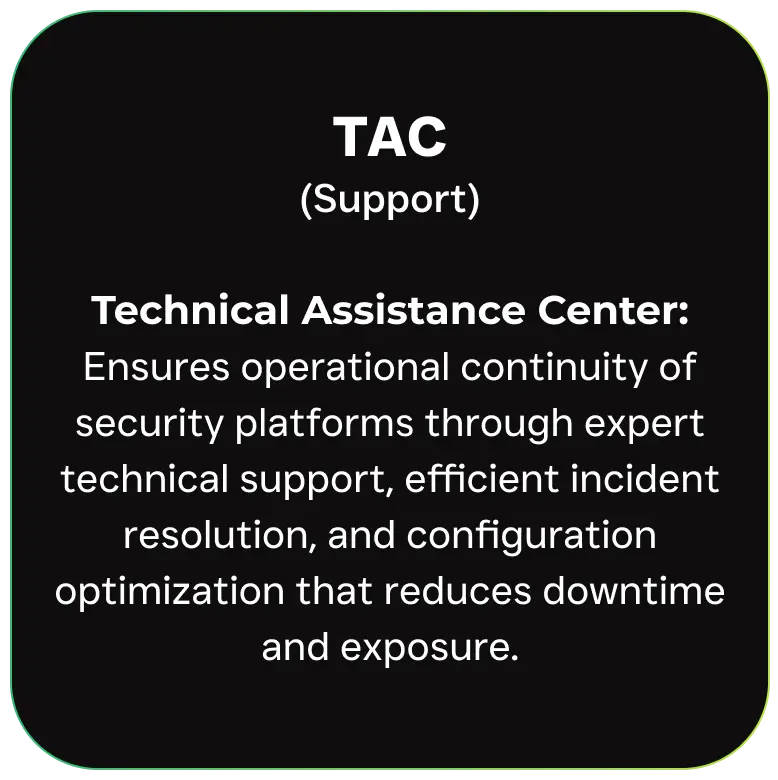
End-to-End Services: TAC, PSU, NOC
Technical Assistance Center
It ensures the operational continuity of security platforms through specialized technical support, efficient failure resolution, and configuration optimization to reduce risks and downtime.
PSU (Implementation)
Professional Services Unit
Design and implement robust and scalable cybersecurity solutions that protect the client’s infrastructure, ensuring best practices and efficient integration with their technological ecosystem.
Minimized downtime with quicker recovery through optimized configurations and enhanced performance.
Your complete ecosystem of cybersecurity solutions
designed, supported, and monitored by experts.


