The threat actors group named BlackCat (also known as ALPHV) has been observed using malvertising techniques, to distribute their malware via web pages spoofing the official website of WinSCP, a file transfer application.
According to observations made by the Trendmicro team, malicious actors have recently been abusing malvertising to distribute malware via websites masquerading as legitimate sites. In the specific case involved in this article, the website used by malicious actors is WinSCP, an open-source Windows file transfer application.
The use of advertising platforms by malicious actors to trick users is not a new practice, due to the widespread use of platforms such as Google Ads by companies to promote their applications in a better way. This is no different for WinSCP, with approximately 400,000 downloads per week.
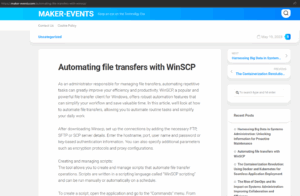
The malicious group BlackCat has been using WinSCP-specific malvertisements in search engines such as Bing or Google. When the user searches for “WinSCP Download” the malicious advertisement is displayed to the user, who upon clicking on it is redirected to a website which displays a tutorial of the application in question.
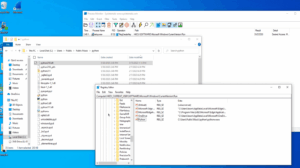
Once the user is redirected to the website impersonating the original site, they will find a download button which will proceed to download an ISO file from an infected WordPress web page. The downloaded files are identified as “setup.exe” and “msi.dll” the former is the lure for the user to run and the latter is the malware dropper activated by the executable.
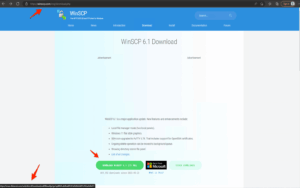
When the “setup.exe” file is executed, it calls the “msi.dll” file which extracts a Python folder from the RCDATA DLL section as would be the case in a genuine WinSCP installer. Between the two Python installations is a trojanized “python310.dll” file with the purpose of creating persistence on the compromised systems using an execution key named “Python” and the value “C:UsersPublicMusicpythonpythonw.exe”.
When the pythonw.exe executable starts, it loads a modified python320.dll which contains a Cobalt Strike beacon that starts a connection to the attackers’ command and control (C2) server. From here the main beacon module is obtained.
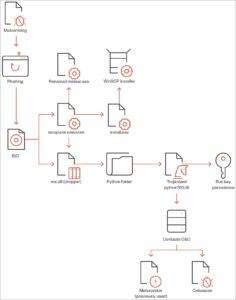
Next, multiple scheduled tasks are created on the compromised systems to maintain persistence on them. At the same time, once the Cobalt strike module is running on the system, the actions to be taken can be varied by running additional scripts to search for tools that allow lateral movement and allow the attacker to further compromise the system.
As observed by trendmicro researchers, the malicious group BlackCat makes use of some extra tools for the later phases of the attack, among these tools, we can highlight the ones listed below:
- AdFind: Command-line tool used to retrieve Active Directory (AD) information.
- PowerShell commands used to collect user data, extract ZIP files, and execute scripts.
- AccessChk64: Command-line tool used for user and group permissions recognition.
- Findstr: command line tool used to search for passwords within XML files.
- PowerView: PowerSploit script used for AD recognition and enumeration.
- Python scripts used to run the LaZagne password recovery tool and obtain Veeam credentials.
- PsExec, BitsAdmin and Curl, used for lateral movement.
- AnyDesk: legitimate remote management tool abused to maintain persistence.
- KillAV BAT script used to disable or bypass anti-virus and anti-malware programs.
- PuTTY secure copy client used to exfiltrate information collected from the compromised system.
It is worth mentioning the use, by the malicious group, of the anti-virus and anti-EDR detection tool called “Terminator”, a tool that, according to what is indicated in the Russian forums where it is traded, could bypass Windows security tools, through a BYOVD attack; with the purpose of manipulating the protection provided by the agents.
Recommendations
- Implement an awareness and training program on phishing and its consequences, as well as its identification.
- Implement a centralized logging system to collect and analyze logs from various network devices and systems.
- Have defined normal network traffic for normal operations, to detect any alteration or abnormal behavior of the same.
- Implement intrusion detection systems (IDS) to detect command and control activity, as well as any other potentially malicious network activity.
- Do not click on suspicious links or advertisements and avoid visiting unsafe websites.
- Use firewalls and content filtering to block access to known malicious websites and services.
IOC
SHA-256 | Command and Control |
| 25467df66778077cc387f4004f25aa20b1f9caec2e73b9928ec4fe57b6a2f63c | 167.88.164.141 = 91. C&C Server |
| 4a4d20d107ee8e23ce1ebe387854a4bfe766fc99f359ed18b71d3e01cb158f4a | https://167.88.164.40/python/pp2 = 91. C&C Server |
| 13090722ba985bafcccfb83795ee19fd4ab9490af1368f0e7ea5565315c067fe | https://172.86.123.127:8443/work2z = 91. C&C Server |
| 8859a09fdc94d7048289d2481ede4c98dc342c0a0629cbcef2b91af32d52acb5 | https://172.86.123.127:8443/work2 |
| bacbe893b668a63490d2ad045a69b66c96dcacb500803c68a9de6cca944affef | https://172.86.123.226:8443/work3z = 91. C&C Server |
| c7a5a4fb4f680974f3334f14e0349522502b9d5018ec9be42beec5fa8c1597fe | https://172.86.123.226:8443/work3 |
| 3ce4ed3c7bd97b84045bdcfc84d3772b4c3a29392a9a2eee9cc17d8a5e5403ce | https://193.42.32.58:8443/work2z = 91. C&C Server |
| 21e7bcc03c607e69740a99d0e9ae8223486c73af50f4c399c8d30cce4d41e839 | https://193.42.32.58/python/pp |
| e5db80c01562808ef2ec1c4b8f3f033ac0ed758d | https://193.42.32.58:8443/zakrep |
| cfbde85bdb62054b5b9eb4438c3837b9f1a69f61 | https://104.234.147.134/python/pp3.py = 91. C&C Server |
| 3b14559a6e33fce120a905fde57ba6ed268a51f1 | http://45.12.253.50:447/work2 |
| aae1b17891ec215a0e238f881be862b4f598e46c | https://45.66.230.240/python/pp3.py = 91. C&C Server |
| c82b28daeb33d94ae3cafbc52dbb801c4a5b8cfa | https://45.66.230.240:8443/work1 |
| d2663fc6966c197073c7315264602b4c6ba9c192 | http://45.66.230.240/python/pp |
| c7568d00ae38b3a4691a413ed439a0e3fb5664b1 | https://firstclassbale.com/python/pp3.py = 91. C&C Server |
| 61e41be7a9889472f648a5a3d0b0ab69e2e056c5 | URLs acceded by Trojan.BAT.COBEACON.AO.dldr |
| 69ffad6be67724b1c7e8f65e8816533a96667a36 | http://104.234.147.134/python/python.zip |
| c1516915431cb55703b5a88d94ef6de0ac67190a | https://167.88.164.40/python/python.zip = 79. Disease Vector |
| a7b1853348346d5d56f4c33f313693a18b6af457 | http://172.86.123.226/python/python.zip = 79. Disease Vector |
| ac8e3146f41845a56584ce5e8e172a56d59aa804 | https://45.66.230.240/python/python.zip |
| e5d434dfa2634041cdbdac1dec58fcd49d629513 | https://closeyoueyes.com/python/python.zip |
| 42da9e9e3152c1d995d8132674368da4be78bf6a | https://firstclassbale.com/python/python.zip |
| 5cbb6978c9d01c8a6ea65caccb451bf052ed2acd | https://167.88.164.40/python/unzip.bat = 79. Disease Vector |
| a9310c3f039c4e2184848f0eb8e65672f9f11240 | http://172.86.123.226/python/unzip.bat = 79. Disease Vector |
| 5e36a649c82fa41a600d51fe99f4aa8911b87828 | http://104.234.147.134/python/unzip.bat |
| 5263a135f09185aa44f6b73d2f8160f56779706d | https://45.66.230.240/python/unzip.bat |
| 75d02e81cc326e6a0773bc11ffa6fa2f6fa5343e | https://closeyoueyes.com/python/unzip.bat |
| 9d85cb2c6f1fccc83217837a63600b673da1991a | https://firstclassbale.com/python/unzip.bat |
| 2f2eb89d3e6726c6c62d6153e2db1390b7ae7d01 | https://167.88.164.40/python/pp3.py = 79. Disease Vector |
| 7d500a2cd8ea7e455ae1799cb4142bb2abac3ae1 | http://172.86.123.226/python/pp3.py = 79. Disease Vector |
| 0362c710e4813020147f5520a780a15ef276e229 | ccloseyoueyes.com/python/pp3.py |
| fb2ef2305511035e1742f689fce928c424aa8b7d | http:////bigallpack.com/union/desktop |
| 7874d722a6dbaef9e5f9622d495f74957da358da | Distribution URLs |
| 06e3f86369046856b56d47f45ea2f7cf8e240ac5 | https://cuororeresteadntno.com/how-to-work-with-ftp-ftps-connection-through-winscp/ = 78. Malware Accomplice |
| 36b454592fc2b8556c2cb983c41af4d2d8398ea2 | https://airplexacrepair.com/the-key-to-secure-remote-desktop-connections-a-comprehensive-guide/ = 78. Malware Accomplice |
| 337ca5eefe18025c6028d617ee76263279650484 | https://maker-events.com/automating-file-transfers-with-winscp/ = 78. Malware Accomplice |
| e862f106ed8e737549ed2daa95e5b8d53ed50f87 | |
| 2a85cdfb1c3434d73ece7fe60d6d2d5c9b7667dd | |
| d883be0ee79dec26ef8c04e0e2857a516cff050c | |
| a0f1a8462cb9105660af2d4240e37a27b5a9afad | |
| ab0eade9b8d24b09e32aa85f78a51b777861debc | |
| 0cc0e1cbf4923d2ce7179064c244fe138dcb3ce8 | |
| 3789a218c966f175067242975e1cb44abdef81ec | |
| 83c5f8821f9a07e0318beaa4bcf0b7ef21127aa8 | |
| 08f63693bb40504b71fe3e4e4d9e7142c011aeb1 | |
| b34bb1395199c7b168d9204833fdfd13d542706d | |
| 5c6aa1a5bd7572ac8e91eaa5c9d6096f302f775b | |
| 9480a79b0b6f164b1148c56f43f3d505ee0b7ef3 | |
| 7874d722a6dbaef9e5f9622d495f74957da358da | |
| 9b1ebbe03949e0c16338595b1772befe276cd10d | |
| 801950ed376642e537466795f92b04e13a4fcc2a | |
| 1ca4e3fdcdf8a9ab095cfa0629750868eb955eb7 | |
| 42920e4d15428d4e7a8f52ae703231bdf0aec241 | |
| 06e3f86369046856b56d47f45ea2f7cf8e240ac5 | |
| f42e97901a1a3b87b4f326cb9e6cbdb98652d900 | |
| d125c4f82e0bbf369caf1be524250674a603435c | |
| 03d7bc24d828abaf1a237b3f418517fada8ae64f | |
| c133992ea87f83366e4af5401a341365190df4e7 | |
| b35be51d727d8b6f8132850f0d044b838fec001d | |
| fd84cf245f7a60c38ac7c92e36458c5ea4680809 | |
| 946c0a0c613c8ac959d94bb2fd152c138fc752da | |
| 7b3051f8d09d53e7c5bc901262f5822f1999caae | |
| eeff22b4a442293bf0f5ef05154e8d4c7a603005 | |
| 2547d2deedc385f7557d5301c19413e1cbf58cf8 | |
| 0437f84967de62d8959b89d28a56e40247b595d8 | |
| 105d33c00847ccd0fb230f4a7457e8ab6fb035fc | |
| 5831b3a830690c603fd093329dce93b9a7e83ad3 | |
| a5c164b734a8b61d8af70257e23d16843a4c72e3 | |
| 1aff9fd8fdc0eae3c09a3ee6b4df2cdb24306498 | |
| 3d4051c65d1b5614af737cb72290ec15b71b75bd | |
| a116ef48119c542a2d864f41dbbb66e18d5cd4e6 | |
| 508e7522db24cca4913aeed8218975c539d3b0a4 | |
| 72603dadebc12de4daf2e12d28059c4a3dcf60d0 | |
| 930bd974a2d01393636fdb91ca9ac53256ff6690 | |
| a9a03d39705bd1d31563d7a513a170c99f724923 | |
| c14bd9ad77d8beca07fb17dc34f8a5f636e621b5 | |
| 01b122eb0edb6274b3743458e375e34126fd2f9a | |
| b98bb7b4c3b823527790cb62e26d14d34d3e499b | |
| 381058a5075ce06605350172e72c362786e8c5e3 | |
| 75e9d507b1a1606a3647fe182c4ed3a153cecc2c | |
| cd485054625ea8ec5cf1fe0e1f11ede2e23dde00 | |
| c9cdfdc45b04cca45b64fedca7c372f73b42cab2 | |
| 31d4dadd11fe52024b1787a20b56700e7fd257f8 | |
| 0fe306dc12ba6441ba2a5cab1b9d26638c292f9c | |
| bc0fb6b220045f54d34331345d1302f9a00b3580 | |
| b4f59fe2ee3435b9292954d1c3ef7e74c233abea | |
| aee0b252334b47a6e382ce2e01de9191de2e6a7a | |
| 92673b91d2c86309f321ade6a86f0c9e632346d8 | |
| de7fb8efa05ddf5f21a65e940717626b1c3d6cb4 | |
| 5f455dcdca66df9041899708289950519971bb76 | |
| 5ed1b9810ee12d2b9b358dd09c6822588bbb4a83 | |
| c779a4a98925bc2f7feac91c1867a3f955462fc2 | |
| cb358aa4ed50db8270f3ee7ea5848b8c16fa21fe | |
| 5ec6b30dacfced696c0145a373404e63763c2fa8 | |
| f2f5137c28416f76f9f4b131f85252f8273baee8 | |
| 12534212c7d4b3e4262edc9dc2a82c98c2121d04 | |
| bc09ee8b42ac3f6107ab5b51a2581a9161e53925 | |
| 152400be759355ec8dd622ec182c29ce316eabb1 | |
| 379e497d0574fd4e612339440b603f380093655c | |
| 141c7b9be4445c1aad70ec35ae3fe02f5f8d37ac | |
| 27e9e6a54d73dcb28b5c7dfb4e2e05aaba913995 | |
| ad981cd18f58e12db7c9da661181f6eb9a1754f3 | |
| 4829eaa38bd061773ceefe175938a2c0d75a75f3 | |
| b0d61d1eba9ebf6b7eabcd62b70936d1a343178e | |
| 014c277113c4b8c4605cb91b29302cdedbc2044e |