Recent research reveals that the group of malicious actors behind Akira ransomware, who initially targeted Windows systems, have now turned their attention to Linux systems and are actively targeting multiple organizations worldwide.
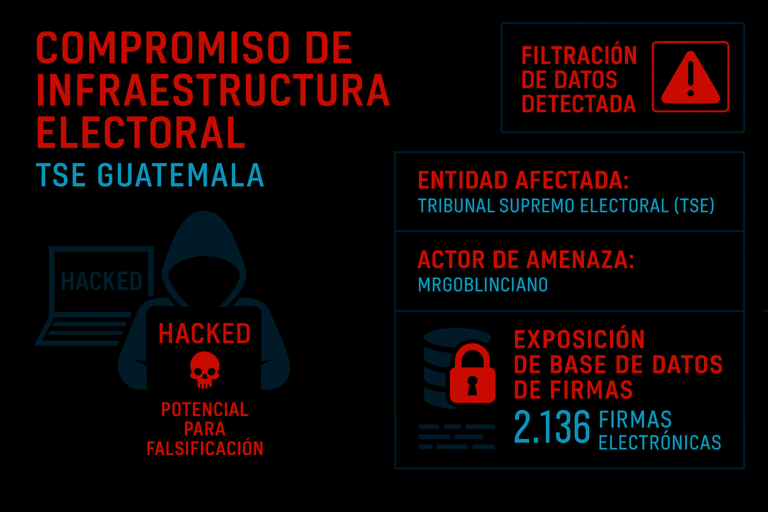
The group of cybercriminals known as Akira was first observed in April 2023, with 46 organizations compromised by them since then. This malicious group leaks and encrypts the information of targeted organizations using the double extortion technique.
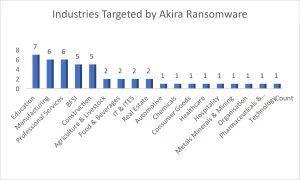
Akira’s target organizations include a wide range of sectors, including education, banking, financial services and insurance, manufacturing, professional services, and many others. The most affected region is North America, with most cases occurring in the United States.
Like any other ransomware group, Akira’s main objective is to steal sensitive information from compromised networks, then encrypt specific targeted files and finally make a ransom demand for the encrypted information, which can be up to several million dollars.
An increase in the ID Ransomware search shows, as previously mentioned, the increasing activity of Akira against companies worldwide, with records of up to 30 new victims in the United States alone.

The Linux variant of the Akira ransomware is a 64-bit executable file of Executable and Linkable Format or ELF. For its execution the attacker needs to provide specific parameters as below.
- “-p” / “-encryption_path” – Path or files/folder to encrypt.
- “-s” / “-share_file” – Path of the network share to be encrypted.
- “-n” / “-encryption_percent” – Percentage of files to encrypt.
- “-fork” – Creation of child processes, for encryption.
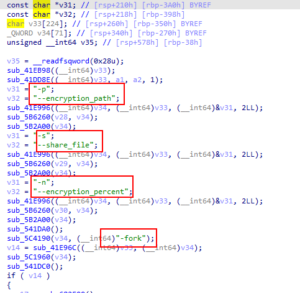
Of these parameters, “-n” is of great interest because it would be inversely related to the encryption speed, that is, the total time it would take the ransomware to encrypt the files in the compromised systems, so that the lower the percentage to encrypt, the higher the encryption speed, this however creates a problem for the attacker because if the percentage of encryption is very low, the compromised user could recover a large amount of this data without paying the ransom demanded.
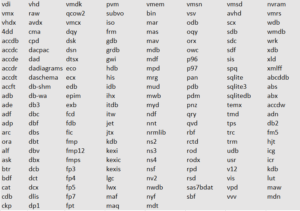
Akira ransomware loads a list of file extensions it targets for encryption and appends the extension “.akira” to each of the compromised files. Among the extensions targeted by Akira, you can see the ones listed below.
As exposed by Cybel, prior to the encryption process Akira ransomware loads a default RSA public key for file encryption on compromised systems and leverages various symmetric key algorithms for file encryption, such as AES, CAMELLIA, IDEA-CB and DES.
The symmetric key is used to encrypt the victims’ files and then encrypted with the RSA public key. This prevents access to the decryption key unless the private RSA decryption key, which only attackers possess, is available.

After all files matching the extensions listed by the group. The encrypted ransomware note is created in each of the compromised folders inside the victim’s device.

This is another example of ransomware groups that initially focused on attacks on Windows systems being seduced to change their target, as in this case with Linux systems, which in turn underlines the increasing vulnerability of these systems to cyber threats.
Recommendations
Some essential recommendations as a first line of defense against this type of malicious actions are:
- Perform regular backups of all systems and keep these backups offline or on a separate network.
- Keep all systems constantly updated, if possible, enable automatic software updates so that important updates are not overlooked.
- As far as possible, refrain from opening untrusted e-mail links and attachments without verifying their authenticity.
- Raise awareness and educate users about common social engineering tactics, such as deception, emotional manipulation, and the use of personal information.
- Develop clear policies and authentication procedures for handling requests for sensitive information or configuration changes.
IOC
| Indicator | Type |
| 302f76897e4e5c8c98a52a38c4c98443 | MD5 |
| 9180ea8ba0cdfe0a769089977ed8396a68761b40 | SHA1 |
| 1d3b5c650533d13c81e325972a912e3ff8776e36e18bca966dae50735f8ab296 | SHA256 |