Recently, experts from Check Point’s research team discovered a series of highly targeted espionage attacks in the Libyan region. These espionage attacks make use of a new custom modular backdoor called Stealth Soldier.
Stealth Soldier is an undocumented backdoor that mainly performs surveillance functions such as file exfiltration, screen and microphone recording, keystroke logging and browser information theft, according to Check Point report.
The most recent version of the malware (version 9) was probably used in February 2023, while the oldest version discovered by the researchers (version 6) dates to October 2022.
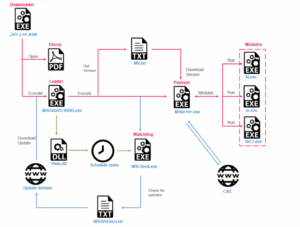
Attacks begin when potential targets download fake binary files that are delivered via social engineering attacks. The intermediate payloads act as a conduit to retrieve Stealth Soldier, while displaying an empty PDF file as a decoy. According to experts, the infection chain is complex and includes six files downloaded from the C&C server.
Below are the main files used in the infection chain:
- Loader (MSDataV5.16945.exe) – Downloads PowerPlus, an internal module for executing PowerShell commands, and uses it to create persistence for the watchdog. Runs the final Stealth Soldier payload.
- Watchdog (MSCheck.exe) – Periodically checks for an updated version of the loader and runs it. Persistent using Schedule Task and the Registry Run key.
- Payload (MShc.txt) – Collects data, receives commands from the C&C server and executes modules.
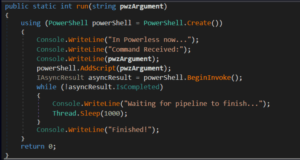
The downloader obtains and opens an empty decoy PDF file from the command and control (C2) server and then downloads a filecloud loader. The loader downloads a .NET module called PowerPlus and executes PowerShell code. PowerPlus is used to execute two commands, one to maintain persistence and the other to query details about the task in a file called DRSch.
The process involves the use of a watchdog as an update mechanism. In the last stage of the infection chain, the malware decrypts the payload before executing it as shellcode, which loads the payload and passes execution to its main logic.
The malware supports different types of commands, some of them in the form of plugins that are downloaded from C2. Other commands are modules within the malware.
“The research suggests that the attackers behind this campaign are politically motivated and are using Stealth Soldier malware and a significant network of phishing domains to conduct surveillance and espionage operations against Libyan and Egyptian targets.” Check Point concludes. “Given the modularity of the malware and the use of multiple stages of infection, it is likely that attackers will continue to evolve their tactics and techniques and deploy new versions of this malware in the near future. Finally, our analysis revealed a connection to the previously exposed Eye on the Nile campaign.”
Eye on the Nile
Researchers noted that Stealth Soldier’s infrastructure has some overlaps with the infrastructure of The Eye on the Nile, a campaign targeting journalists and human rights activists in Egypt in 2019. Experts suspect the recent attack could be linked to the same threat actor.
Amnesty International’s 2019 report describes how Egyptian civil organizations and individuals were targeted by sophisticated phishing attacks using third-party apps, such as Google and Yahoo, to steal sensitive information and monitor their activities. A follow-up report Eye on the Nile uncovered the background of this operation, traced its origin, and connected it to an Android backdoor focused on surveillance.
Throughout the analysis of the Stealth Soldier campaigns, we were able to identify several infrastructure overlaps with known Eye on the Nile domains. This is in addition to the narrow regional targeting and similar phishing domain naming patterns.
IOC’s
| Indicator | Description |
| Domain | filestoragehub[.]live |
| Domain | customjvupdate[.]live |
| Domain | filecloud[.]store |
| Domain | webmailogemail[.]com |
| Domain | loglivemail[.]com |
| Domain | 2096[.]website |
| IP | 185.125.230.216 |
| IP | 185.125.230.116 |
| IP | 94.156.33.228 |
| IP | 94.156.33.229 |
| IP | 185.125.230.224 |
| IP | 185.125.230.220 |
| Hashes | 2cad816abfe4d816cf5ecd81fb23773b6cfa1e85b466d5e5a48112862ceb3efb |
| Hashes | 05db5e180281338a95e43a211f9791bd53235fca1d07c00eda0be7fdc3f6a9bc |
| Hashes | b9e9b93e99d1a8fe172d70419181a74376af8188dcb03249037d4daea27f110e |
| Hashes | d57fc4e8c14da6404bdcb4e0e6ac79104386ffbd469351c2a720a53a52a677db |
| Hashes | e7794facf887a20e08ed9855ac963573549809d373dfe4a287d1dae03bffc59f |
| Hashes | 8c09a804f408f7f9edd021d078260a47cf513c3ce339c75ebf42be6e9af24946 |
| Hashes | df6a44551c7117bc2bed2158829f2d0472358503e15d58d21b0b43c4c65ff0b4 |
| Hashes | e546d48065ff8d7e9fef1d184f48c1fd5e90eb0333c165f217b0fb574416354f |
| Hashes | a43ababe103fdce14c8aa75a00663643bf5658b7199a30a8c5236b0c31f08974 |
| Hashes | c0b75fd1118dbb86492a3fc845b0739d900fbbd8e6c979b903267d422878dbc6 |
| Hashes | cb90a9e5d8b8eb2f81ecdbc6e11fba27a3dde0d5ac3d711b43a3370e24b8c90a |
| Hashes | d6655e106c5d85ffdce0404b764d81b51de54447b3bb6352c5a0038d2ce19885 |
| Hashes | b94257b4c1fac163184b2d6047b3d997100dadf98841800ec9219ba75bfd5723 |
| Hashes | 7bfe2a03393184d9239c90d018ca2fdccc1d4636dfb399b3a71ea6d5682c92bd |