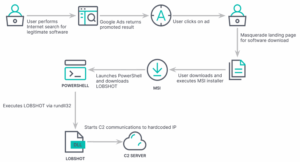
New backdoor and credential stealer masquerades as a legitimate software download as part of an elaborate cyberattack campaign. This campaign is part of the trend of attackers using malvertising as initial access for ransomware and other malicious activities.
One of LOBSHOT’s main capabilities is its hVNC (Hidden Virtual Network Computing) component. This type of module allows direct, unmonitored access to the machine. This feature continues to be successful in circumventing fraud detection systems and is often incorporated into many popular families in the form of plugins.
MALVERTISING
Earlier this year, multiple infections were observed with an interesting chain of events aimed at executing an unknown hVNC malware, which has been dubbed LOBSHOT. At the same time, similar infection chains were observed in the security community, where users looking for legitimate software downloads ended up receiving illegitimate software through promoted Google ads.

The malware campaign is attributed to malicious actors known as TA505, based on the infrastructure historically connected to this group. TA505 is a financially motivated cybercrime syndicate with ties to activity groups tracked under the names Evil Corp, FIN11 and Indrik Spider.
This latest development is quite significant as it is a sign that TA505, who are associated with the Dridex Banking Trojan, are expanding their arsenal of malware to carry out information theft and financial fraud.
LOBSHOT, samples of which have been recorded since July 2022, is known to be distributed via fake Google ads from legitimate tools such as AnyDesk that are hosted on a network of similar landing pages maintained by the operators. The malware incorporates dynamic import resolution, anti-emulation control, and string obfuscation to evade detection by security software.
Once installed, it makes changes to the Windows Registry and thus configures the persistence and data diversion of more than 50 cryptocurrency wallet extensions present in web browsers such as Google Chrome, Microsoft Edge, and Mozilla Firefox.
One of the capabilities of LOBSHOT is, as previously mentioned, the ability to access the compromised host through an hVNC module and stealthily perform actions without even drawing the victim’s attention. While this type of malware may seem small, they end up including significant functionality that helps malicious actors act swiftly during the initial access stages with fully interactive remote control.
It is important to note the large increase in the adoption of malvertising and search engine optimization poisoning as techniques aimed at redirecting users to fake websites through which Trojanized installers of popular software are downloaded.