A vulnerability has recently been discovered in the latest version of Microsoft Teams, which would allow malware to be introduced into any organization that makes use of Microsoft Teams with its default settings. This is achieved by circumventing client-facing security controls.
Microsoft Teams has recently become one of the most widely adopted services by organizations as a collaboration and communication platform. This cloud-based Microsoft 3645 service currently has 280 million active monthly users, making it a desired target for malicious actors.
Due to the popularity of these services, members of Jumpsec have investigated that resulted in the discovery of a vulnerability that would allow any user with a Microsoft account to achieve “outside leases”, which refers to any business or organization that makes use of Microsoft Teams.
The attack
The attack requires that Microsoft Teams is running with default settings, which allows communication with Microsoft Teams accounts outside the company, this communication bridge by itself, may be sufficient for the execution of social engineering or phishing attacks, however, the method that the team found is more powerful because it allows sending payload directly to the target inbox.
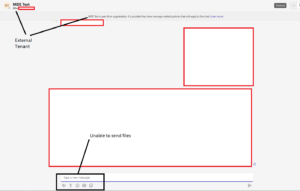
Microsoft Teams has client-side protections in place to block file delivery from external tenant accounts, however, as exposed by the team, there is a way around this restriction, by internally and externally changing the recipient ID in the POST request of a message, so the system is fooled and takes an external user as an internal user.
According to Jumpsec Labs, “When the payload is sent this way, it is hosted on a Sharepoint domain, and the target downloads it from there. However, it appears in the recipient’s inbox as a file, not as a link.” Upon testing the described technique, the researchers were able to successfully send a command-and-control payload to the target organization’s inbox.
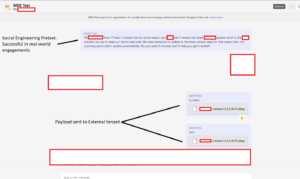
The seriousness of this attack lies in its ability to circumvent existing security measures by also being able to fool trained phishing detection users, allowing attackers a fairly simple way to infect any organization using Microsoft Teams with default settings.
Another option for the attacker is to register a domain like that of the target organization in Microsoft 365, as in this case, the messages would appear to come from someone within the organization itself and not some other external organization, which would increase the likelihood of users downloading these malicious files. This vulnerability has enormous potential scope and could be used by malicious actors to bypass traditional payload delivery security controls,
While, the discovery was reported to Microsoft, they mentioned that this issue was not something they saw as requiring an immediate fix. The recommended action for organizations that use Microsoft Teams and do not need to maintain regular communication with external tenants is to disable this feature from “Microsoft Teams Admin Center > External Access.”