New campaign attributed to APT42, also known as “Charming Kitten” or TA453, has been recently discovered by researchers, these campaigns make use of the malware called “NokNok” which can compromise macOS systems.
According to observations made, the campaign in question started in May, differing from previous campaigns using LNK files in the infection chain, these implement payloads instead of malicious Microsoft Word documents, typical of the malicious actor group, in past attacks.
The malicious actor group TA453, also known as Charming Kitten, is a group linked to the Iranian state, as reported by Google, more precisely to the IRGC (Islamic Revolutionary Guard Corps). As noted by mandiant, the group is said to be behind at least 30 operations across 14 countries. Its activities date back to at least 2015.
As mentioned earlier, the malicious actor group has changed its modus operandi, making use of LNK files to deploy payloads to compromised systems, instead of malicious Microsoft Word documents (a common practice of the group).
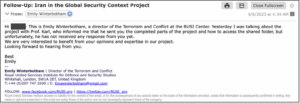
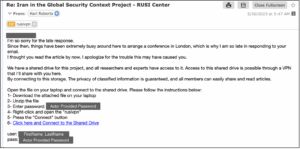
The chain of events starts with an email from the group to the target user, in which they impersonate nuclear security experts from the Royal United Services Institute (RUSI). The first contact is made via a benign email, where the malicious actors request permission to send a draft to the victim, this being the malicious link, which redirects the victim to a Dropbox URL.
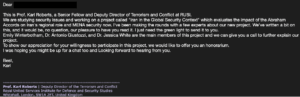
This link contains an encrypted .rar file, which contains an .lnk file (Abraham Accords & MENA.rar and Abraham Accord & MENA.pdf.ink, respectively) these files are used for malware deployment. The .lnk file uses PowerShell to download additional items from a cloud host.
The final payload used is a backdoor that allows executing remote operator commands, the backdoor in question is called “GorjolEcho” which communicates via HTTPS encrypted by AES. To remain hidden and not raise suspicion, GorjolEcho opens a PDF on a relevant topic of the initial discussion that the malicious actor has with the victim.
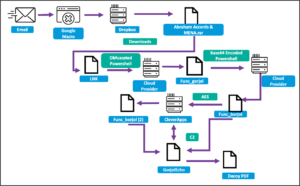
GorjolEcho then proceeds to encode, encrypt, and leak information to the malicious actors’ command and control server.
Initially, the file sent by TA453 to the victim did not run on Apple devices, however, about a week after the initial contact, the malicious actors contacted the victim again with macOS devices, with a new infection string that appears to be a link for a VPN connection. As shown below.
The link hosts a .zip file containing the first-stage malware infection against macOS devices, along with a set of instructions. This .zip file contains the Mach-O binary which executes an Apple script, it uses cURL to download a file from the cloud, the address resolves to 144.217.129[.]176 which is an OVH IP.
For the second stage, the script retrieves the “NokNok” payload which establishes a backdoor on the compromised machine’s system. NokNok, named after proofpoint, generates a system identifier, and then uses four bash script modules to establish persistence on the system. The four modules are described as Process, Information, Application, Persistence.
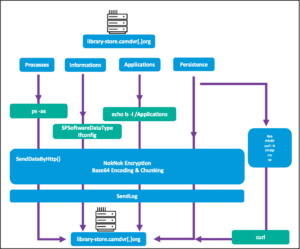
Once on the system “NokNok” collects system information, including operating system version, running processes, installed software, the information module also makes use of “ifconfig” to collect network information. The collected information is base64 encoded and stored in result.txt for further filtering.
According to these observations, both NokNok and GorjolEcho are believed to be focused on additional espionage operations through unobserved modules, based on similarities in the code of GhostEcho, whose backdoor also featured information modules for screen capture, command execution, and cleaning up any traces of the infection.
In turn, this type of campaign shows the adaptability of AP453 (Charming kitten) to the systems to which the campaigns are directed. Capable of compromising macOS systems when needed. At the same time, it highlights the growing threat against these systems in new campaigns capable of targeting different operating systems.
IOC
| Indicator | Type | context |
| 464c5cd7dd4f32a0893b9fff412b52165855a94d193c08b114858430c26a9f1d | SHA256 | Dropper (Abraham Accords & MENA.pdf.lnk) |
| ddead6e794b72af26d23065c463838c385a8fdff9fb1b8940cd2c23c3569e43b | SHA256 | Archive (Abraham Accords & MENA.rar) |
| 1fb7f1bf97b72379494ea140c42d6ddd53f0a78ce22e9192cfba3bae58251da4 | SHA256 | NokNok Backdoor |
| e98afa8550f81196e456c0cd4397120469212e190027e33a1131f602892b5f79 | SHA256 | NokNok aplication module |
| 5dc7e84813f0dae2e72508d178aed241f8508796e59e33da63bd6b481f507026 | SHA256 | NokNok persistence module |
| b6916b5980e79a2d20b4c433ad8e5e34fe9683ee61a42b0730effc6f056191eb | SHA256 | NokNok Process Module |
| acfa8a5306b702d610620a07040262538dd59820d5a42cf01fd9094ce5c3487c | SHA256 | Information module [ADJ1] [CG2] [CG2] [CG2 |
| library-store[.]camdvr[.]org | Host | NokNok C2 |
| 144.217.129[.]176 | IP | NokNok C2 |
| filemanager.theworkpc[.]com | Host | FTP website server |
| fuschia-rhinestone.cleverapps[.]io | Host | GorjolEcho C2 |