A vulnerability in the Service Location Protocol (SLP) could become a weapon that would allow attackers to launch massive denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks against their targets.
Research shows that the vulnerability, identified as CVE-2023-29552, could be exploited by attackers to launch massive, amplified denial-of-service (DoS) attacks with a factor of more than 2,200 times, potentially making it one of the largest amplification attacks ever recorded.
- CVE-2023-29552: Vulnerability in the Service Location Protocol (SLP) which could lead to denial-of-service (DoS) attacks by sending a massive amount of traffic to the victims’ network via amplification attacks. CVSS score: 8.6.
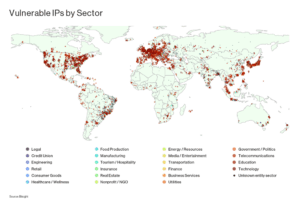
Research as of early February 2023 reports the identification of more than 2,000 organizations globally and more than 54,000 SLP instances, including VMware ESXi Hypervisor, Konica Minolta printers, Planex Routers, IBM Integrated Management Module (IMM), SMCIPMI, among others, which malicious actors could leverage to launch DoS attacks against unsuspecting organizations around the world.
Service Location Protocol (SLP)
A protocol that provides a dynamic configuration mechanism for local area network (LAN) applications. The SLP protocol allows systems on a network to find each other and communicate with each other. This is done by a directory of available services which may include printers, server files, among other network resources.
The SLP protocol works by having a system register with a directory agent, which then makes the system’s services available to other systems on the network. The deamons (programs running in the background) that provide SLP are bound to the default port 427, both UDP and TCP.
While the SLP protocol was not intended to be publicly available on the Internet, it has been found in a variety of instances connected to the Internet. A recent scan of the entire Internet revealed more than 54,000 SLP-speaking instances online, belonging to organizations across numerous sectors and geographies.
Such an attack can produce an amplification factor of over 2,200, resulting in a large-scale denial-of-service (DoS) attack. The prevalence of SLP-based DDoS attacks is expected to increase significantly in the coming weeks as threat actors experiment with the new DDoS amplification vector.
Such an attack can produce an amplification factor of over 2,200, resulting in a large-scale denial-of-service (DoS) attack. The prevalence of SLP-based DDoS attacks is expected to increase significantly in the coming weeks as threat actors experiment with the new DDoS amplification vector.
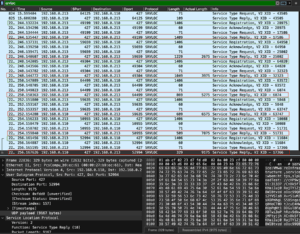
Reflective DoS amplification attack leveraging the CVE-2023-29552
The attack could be divided into four basic steps:
- Step 1: The attacker finds an SLP server on UDP port 427.
- Step 2: The attacker registers services until SLP denies further entry.
- Step 3: The attacker forges a request to that service with the victim’s IP as the source.
- Step 4: The attacker repeats the action of step 3 if the attack is in progress.
The configuration phase of the attack only must occur once to fill the server’s response buffer. The attacker can manipulate both the content and the size of the server response by registering new arbitrary services. During the attack, as shown in the image above, the interaction between the attacker (in green) and the server (in red) would look like a loop of registering services until the server buffer is full, followed by arbitrary fake requests.
Suggestions
- VMware recommends upgrading to a supported version that is not vulnerable to CVE-2023-29552.
- Disable SLP port on systems directly connected to the Internet, or alternatively, filter traffic on UDP and TCP port 427.