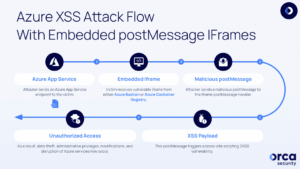
Two high-risk vulnerabilities have recently been found in Azure Bastion and Azure Container Registry services. This vulnerability allows an attacker to get a cross-site script or XSS through iframe-post Messages.
Microsoft Azure offers a diverse range of services that provide organizations with convenient and scalable cloud infrastructure solutions. However, even the most robust systems can fall victim to vulnerabilities, such is the case with the vulnerability we are addressing.
The vulnerability allows an attacker unauthorized access to the victim’s session within the compromised iframe of Azure services.
XSS
A cross-site scripting, or XSS for short, happens when an attacker injects malicious scripts into a trusted website, which are then executed by browser users, which can result in unauthorized access to information, data theft, and in the worst cases, complete system compromise.
In this case, the attackers used the postMessage iframe vulnerability as an entry point to drive the exploitation of XSS flaws.
POSTMESSAGE
The postMessage service is a web API that allows communication between different sources (different domains, protocols, or ports) on a web page. This allows scripts on one page to send messages to another page. The postMessage iframe vulnerability allows an attacker to insert remote servers into endpoints using the iframe tag and ultimately execute malicious JS code that compromises sensitive data.
AZURE BASTION
Azure Bastion is a service that provides a secure and seamless way to access virtual machines in Azure environments. It acts as a jump server, providing a dedicated, hardened gateway to connect to virtual machines securely without exposing them to the public Internet.
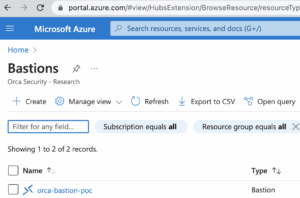
This service works by creating a private Remote Desktop Protocol (RDP) or Secure Shell (SSH) session between local user machines and the Azure virtual machine. Which eliminates the need for a public IP on a VM connection or a VPN.
However, to exploit this vulnerability, a malicious actor would need to perform reconnaissance on different Azure services to locate those vulnerable endopoints embedded in the Azure portal that may have missing X-Frame-Options headers or weak Content Security Policies (CSPs).
Once the attacker successfully embeds the iframe on a remote server, the attacker proceeds to exploit the misconfigured endpoint. Attackers then target the postMessage handler, which handles remote events as postMessages.
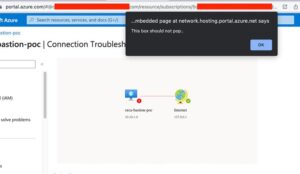
By parsing legitimate postMessages sent to the iframe from porta.azure.com, the attacker can create appropriately crafted payloads to embed the vulnerable iframe on the actor-controlled server and create a postMessage that delivers the malicious payload.
Thus, when a victim visits the compromised endpoint, the malicious postMessage payload is delivered to the embedded iframe, triggering the XSS vulnerability and executing the attacker’s code in the victim’s context.
Successful exploitation of the XSS vulnerability grants the attacker unauthorized access to the victim’s session, on the compromised Azure service. This can lead to serious consequences such as unauthorized access to information, administrator privileges, information theft, unauthorized modifications, or disruption of Azure services.
For Azure Bastion, the vulnerability is in the Azure Network Watcher connection troubleshooter. Due to the incorrect implementation of validation checking, an attacker can make a specially crafted HTML page, which once rendered in the victim’s browser, results in code execution.
As can be seen in the report presented by Orca, the combination of several factors related to poor security have contributed to the vulnerability, allowing attackers to automate the execution of malicious SVG payloads on behalf of the victim.
AZURE CONTAINER REGISTRY
This is a managed cloud service that allows users to deploy, manage and store container images from a centralized location, allowing them to be managed and versioned efficiently.
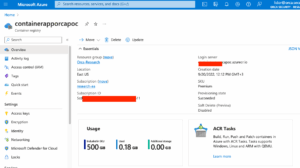
In the case of Azure Container Registry, the vulnerability lies in a piece of HTML code on an unused web page as part of ACR’s Azure Portal extension. According to Orca’s research, the HTML file that allowed the code injection was identified.
Based on observations, the portal’s main page contained an iframe that communicated with postMessages with an HTML file. The communication method was then found to be exploitable due to the lack of an origin check.
Following responsible disclosure of the flaws on April 13 and May 3, 2023, Microsoft deployed security fixes to remediate them. No further action is required by Azure users.



