CISA Releases Nine Industrial Control Systems Advisories
CISA released nine Industrial Control Systems (ICS) advisories on June 29, 2023. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS.
ICSA-23-180-01 Delta Electronics InfraSuite Device Master
ICSA-23-180-02 Schneider Electric EcoStruxure
ICSA-23-180-03 Ovarro TBox RTUs
ICSA-23-180-04 Mitsubishi Electric MELSEC-F Series
ICSMA-23-180-01 Medtronic Paceart Optima System
ICSA-19-120-01 Rockwell Automation CompactLogix 5370 (Update A)
ICSA-20-245-01 Mitsubishi Electric Multiple Products (Update F)
ICSA-22-333-05 Mitsubishi Electric FA Engineering Software (Update B)
ICSA-23-171-02 Enphase Installer Toolkit Android App (Update A)
CISA encourages users and administrators to review the newly released ICS advisories for technical details and mitigations.
CISA Adds Eight Known Exploited Vulnerabilities to Catalog
CISA has added eight new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation.
CVE-2019-17621 D-Link DIR-859 Router Command Execution Vulnerability
CVE-2019-20500 D-Link DWL-2600AP Access Point Command Injection Vulnerability
CVE-2021-25487 Samsung Mobile Devices Out-of-Bounds Read Vulnerability
CVE-2021-25489 Samsung Mobile Devices Improper Input Validation Vulnerability
CVE-2021-25394 Samsung Mobile Devices Race Condition Vulnerability
CVE-2021-25395 Samsung Mobile Devices Race Condition Vulnerability
CVE-2021-25371 Samsung Mobile Devices Unspecified Vulnerability
CVE-2021-25372 Samsung Mobile Devices Improper Boundary Check Vulnerability
These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Note: To view other newly added vulnerabilities in the catalog, click on the arrow in the “Date Added to Catalog” column—which will sort by descending dates.
Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the Known Exploited Vulnerabilities Catalog as a living list of known Common Vulnerabilities and Exposures (CVEs) that carry significant risk to the federal enterprise. BOD 22-01 requires Federal Civilian Executive Branch (FCEB) agencies to remediate identified vulnerabilities by the due date to protect FCEB networks against active threats. See the BOD 22-01 Fact Sheet for more information.
Although BOD 22-01 only applies to FCEB agencies, CISA strongly urges all organizations to reduce their exposure to cyberattacks by prioritizing timely remediation of Catalog vulnerabilities as part of their vulnerability management practice. CISA will continue to add vulnerabilities to the catalog that meet the specified criteria.
2023 CWE Top 25 Most Dangerous Software Weaknesses
The Homeland Security Systems Engineering and Development Institute, sponsored by the Department of Homeland Security and operated by MITRE, has released the 2023 Common Weakness Enumeration (CWE) Top 25 Most Dangerous Software Weaknesses. The CWE Top 25 is calculated by analyzing public vulnerability data in the National Vulnerability Data (NVD) for root cause mappings to CWE weaknesses for the previous two calendar years. These weaknesses lead to serious vulnerabilities in software. An attacker can often exploit these vulnerabilities to take control of an affected system, steal data, or prevent applications from working.
The 2023 CWE Top 25 also incorporates updated weakness data for recent CVE records in the dataset that are part of CISA’s Known Exploited Vulnerabilities Catalog (KEV).
CISA encourages developers and product security response teams to review the CWE Top 25 and evaluate recommended mitigations to determine those most suitable to adopt. Over the coming weeks, the CWE program will be publishing a series of further articles on the CWE Top 25 methodology, vulnerability mapping trends, and other useful information that help illustrate how vulnerability management plays an important role in Shifting the Balance of Cybersecurity Risk.
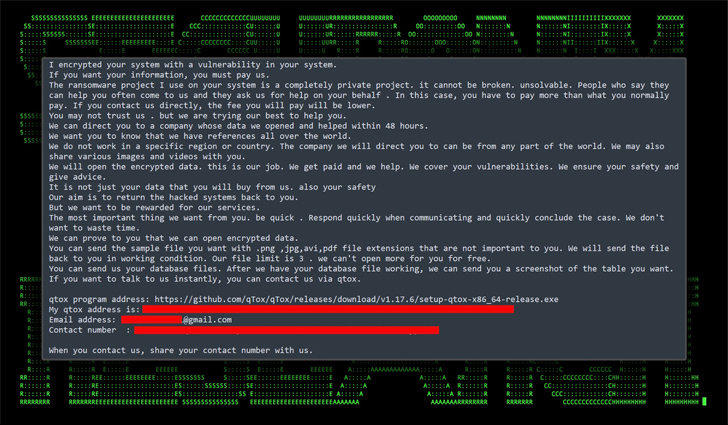
Akira ransomware apunta a Linux
Investigaciones recientes revelan que el grupo de actores maliciosos detrás de Akira ransomware, quienes inicialmente tenían como objetivo a sistemas Windows, ahora han volteado su interés a sistemas Linux y se encuentran activamente dirigiendo ataques contra múltiples organizaciones a nivel mundial. El grupo de ciber criminales conocidos como Akira fue observado por primera vez en […]
Nuevas funcionalidades en Sysmon v15.0

Recientemente Microsoft ha liberado Sysmon v15.0 la cual agrega, entre otras funcionalidades, la nueva opción “FileExecutableDetected”, esta funcionalidad permite detectar cuando se ha creado un archivo ejecutable en los sistemas donde se incorpora. System Monitor o Sysmon, es un servicio presente en los sistemas de Windows que permite el monitoreo y registra actividades dentro del […]
